Difference between revisions of "Create SSH Keys Using Putty"
(Undo revision 27304 by Israel.herrera (talk)) Tag: Undo |
|||
| (3 intermediate revisions by one other user not shown) | |||
| Line 1: | Line 1: | ||
| − | + | {|align=right | |
| − | + | |__TOC__ | |
| − | + | |} | |
| − | + | These steps are handled in a slightly different ways on each operating system. Separate instructions for Microsoft Windows OS variants are listed below. | |
| − | |||
| − | |||
| − | |||
| − | |||
__NOTOC__ | __NOTOC__ | ||
==Prerequisite software== | ==Prerequisite software== | ||
| Line 22: | Line 18: | ||
==Generating your keys== | ==Generating your keys== | ||
| − | + | {{Note|'''Never share your private ssh keys''' even with Support staff. Your private ssh key works as your password and it must be kept in a non-shareable space.|warn}} | |
Now we can generate your key pair. Your key pair consists of two keys, one public and one private. The public key is the one that you will upload to HPG. The private key must be kept secure. Once enabled, this key will allow you to login to HPG directly, so it needs to be stored in a safe place. Treat it as you would treat your HiPerGator or GatorLink password and remember the consequences of facilitating unauthorized access to University systems. | Now we can generate your key pair. Your key pair consists of two keys, one public and one private. The public key is the one that you will upload to HPG. The private key must be kept secure. Once enabled, this key will allow you to login to HPG directly, so it needs to be stored in a safe place. Treat it as you would treat your HiPerGator or GatorLink password and remember the consequences of facilitating unauthorized access to University systems. | ||
| Line 54: | Line 50: | ||
==Enabling Key Access to HPG== | ==Enabling Key Access to HPG== | ||
| + | [[File:HPG_PuTTY.png|Example Connection to HPG using PuTTY | right]] | ||
| − | In order to enable key-based login to HPG, you will need to copy the public key content from the PuTTYgen window into your authorized_keys file on HPG. To do this you will need to login to HPG using your account. You can use any SSH client for this step, but for this tutorial, we will be using PuTTY. Go ahead and start your SSH client and log in to hpg.rc.ufl.edu with your username and password. You should see a command prompt in your home directory. To do this in PuTTY, simply start the application, enter “hpg.rc.ufl.edu", and click "Open" as shown in the figure | + | In order to enable key-based login to HPG, you will need to copy the public key content from the PuTTYgen window into your authorized_keys file on HPG. |
| − | + | #To do this you will need to login to HPG using your account. You can use any SSH client for this step, but for this tutorial, we will be using PuTTY. Go ahead and start your SSH client and log in to hpg.rc.ufl.edu with your username and password. You should see a command prompt in your home directory. | |
| − | + | #To do this in PuTTY, simply start the application, enter “hpg.rc.ufl.edu", and click "Open" as shown in the figure to the right:<br /> | |
| − | + | #Once you click "Open", if this is the first time you have connected to HPG, you will receive a key warning, accept this HPG key to not recive this pop-up in the future. Then enter your GatorLink username and press the enter key. | |
| − | Once you click "Open", if this is the first time you have connected to HPG, you will receive a key warning, accept this HPG key to not recive this pop-up in the future. Then enter your GatorLink username and press the enter key. | + | #Now you can open and edit your authorized_keys file. To do this, type the following into the command prompt and press enter:<br /> |
| − | + | #*<code>nano $HOME/.ssh/authorized_keys</code> | |
| − | Now you can open and edit your authorized_keys file. To do this, type the following into the command prompt and press enter:<br /> | + | #You will now be editing your authorized_keys file. There will likely already be entries for keys that were generated for your account automatically. Please select copy the data from the PuTTYgen window labeled "key" to your clipboard. |
| − | <code>nano $HOME/.ssh/authorized_keys</code> | + | #Use the arrow keys to navigate to the bottom of the list in the authorized_keys file and paste the data from the PuTTYgen window into this file. All the pasted content should be on one line. Please use right click to copy and paste since that will produce the best results. |
| − | + | #After you have pasted the information in the file, press the <code>CTRL</code> and <code>o</code> keys at the same time followed by <code>Enter</code> to write out the file. Then press the <code>CTRL</code> and <code>x</code> keys at the same time to exit the editor.<br /> | |
| − | You will now be editing your authorized_keys file. There will likely already be entries for keys that were generated for your account automatically. Please select copy the data from the PuTTYgen window labeled "key" to your clipboard. Use the arrow keys to navigate to the bottom of the list in the authorized_keys file and paste the data from the PuTTYgen window into this file. All the pasted content should be on one line. | ||
| − | |||
| − | Please use right click to copy and paste since that will produce the best results. After you have pasted the information in the file, press the <code>CTRL</code> and <code>o</code> keys at the same time followed by <code>Enter</code> to write out the file. Then press the <code>CTRL</code> and <code>x</code> keys at the same time to exit the editor.<br /> | ||
Congratulations your key is now authorized to login to your account on HPG. | Congratulations your key is now authorized to login to your account on HPG. | ||
Latest revision as of 13:39, 26 June 2023
These steps are handled in a slightly different ways on each operating system. Separate instructions for Microsoft Windows OS variants are listed below.
Prerequisite software
Here is a list of the software you will need to be installed on your local machine to start using key-based authentication.
- An SSH client (Putty, Tabby, etc.)
- The Windows Putty Agent (pagent.exe)
- The command-line interface (plink.exe)
You can find many of these to download at the putty site:
http://www.chiark.greenend.org.uk/~sgtatham/putty/latest.html
Most of these software applications are contained in the Windows installer (.msi) for PuTTY and that is the recommended approach. If you do not have administrative authority on your PC you can also download a zip file containing all the needed programs. These will need to be extracted into a folder of your choosing.
Generating your keys
Now we can generate your key pair. Your key pair consists of two keys, one public and one private. The public key is the one that you will upload to HPG. The private key must be kept secure. Once enabled, this key will allow you to login to HPG directly, so it needs to be stored in a safe place. Treat it as you would treat your HiPerGator or GatorLink password and remember the consequences of facilitating unauthorized access to University systems.
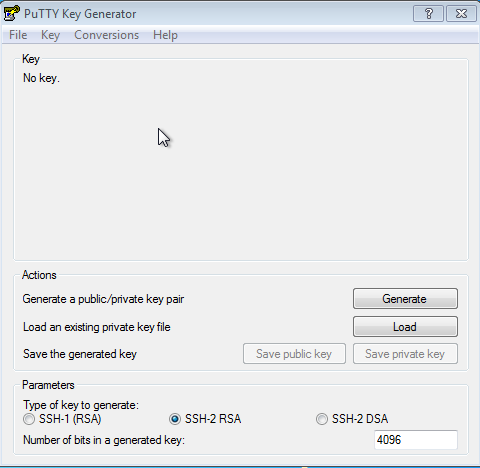
To generate your key pair, start the PuTTYgen program.
Please make sure to select and enter the following options in the lower “Parameters" box: SSH-2 RSA (simply RSA in MobaKeyGen) and 4096 for the number of bits in a generated key.
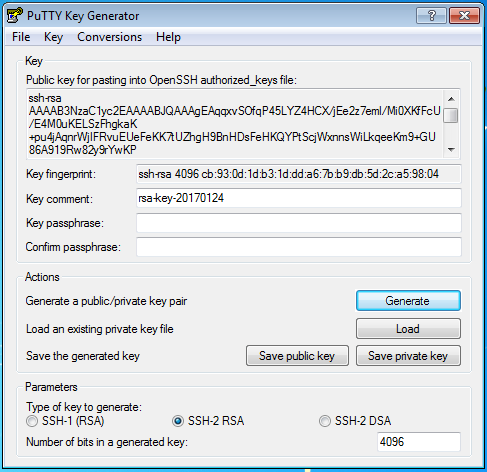
Then click “Generate" to create your key pair. You will be asked to move the mouse around in a random pattern over the window to generate randomness for the key. This may take a bit of time depending on the speed of your computer. Once completed, the public key will be displayed in the “Key" box. The figure below shows what the window looks like after key generation.
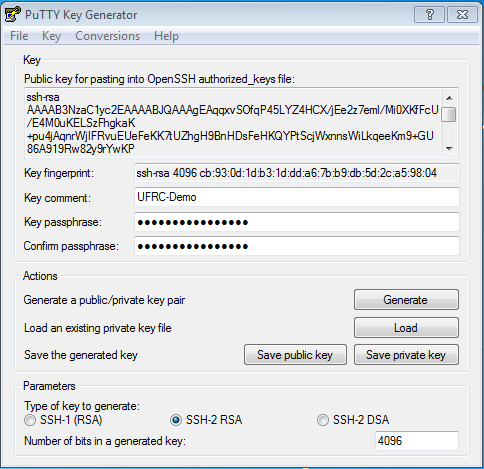
Feel free to edit the “Key Comment" field to give your key a nickname. Then protect your private key with a passphrase. PLEASE DO NOT SKIP THIS STEP!
- Please protect your private key with a strong passphrase. This is what protects your key from other customers and intruders if they ever manage to compromise your system. The figure below shows what the window should look like with the information filled out.
Please choose a passphrase that is easy for you to remember, but hard for another person to guess. If you need resources to help with generating passphrases, please see: http://identity.it.ufl.edu/process/gatorlink/password-tips/
Once your passphrase is set, you can use the “Save private key" and “Save public key" buttons to save your keys. Please make sure to save these in a safe place. The private key should be a “.ppk" file and the public key can be a regular text file “.txt".
By default, the PuTTYgen program converts the key for pasting into an OpenSSH file in the “Key" area of the screen. This is the content you should copy to add to HPG. If you ever need to copy this content again, just click the “Load" button and select your private key file.
Enabling Key Access to HPG
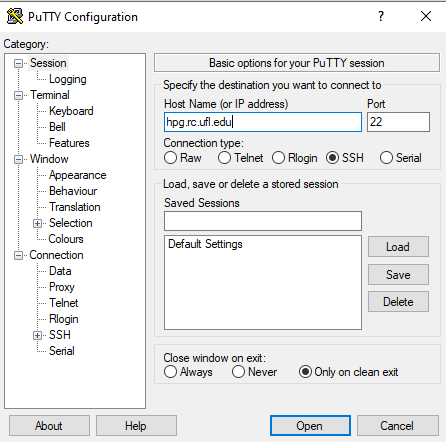
In order to enable key-based login to HPG, you will need to copy the public key content from the PuTTYgen window into your authorized_keys file on HPG.
- To do this you will need to login to HPG using your account. You can use any SSH client for this step, but for this tutorial, we will be using PuTTY. Go ahead and start your SSH client and log in to hpg.rc.ufl.edu with your username and password. You should see a command prompt in your home directory.
- To do this in PuTTY, simply start the application, enter “hpg.rc.ufl.edu", and click "Open" as shown in the figure to the right:
- Once you click "Open", if this is the first time you have connected to HPG, you will receive a key warning, accept this HPG key to not recive this pop-up in the future. Then enter your GatorLink username and press the enter key.
- Now you can open and edit your authorized_keys file. To do this, type the following into the command prompt and press enter:
nano $HOME/.ssh/authorized_keys
- You will now be editing your authorized_keys file. There will likely already be entries for keys that were generated for your account automatically. Please select copy the data from the PuTTYgen window labeled "key" to your clipboard.
- Use the arrow keys to navigate to the bottom of the list in the authorized_keys file and paste the data from the PuTTYgen window into this file. All the pasted content should be on one line. Please use right click to copy and paste since that will produce the best results.
- After you have pasted the information in the file, press the
CTRLandokeys at the same time followed byEnterto write out the file. Then press theCTRLandxkeys at the same time to exit the editor.
Congratulations your key is now authorized to login to your account on HPG.
Note: You can also use a text editor in a terminal or a console session in Open OnDemand to edit ~/.ssh/authorized_keys file.
Using Pageant to create persistent key sessions
In order to take the most advantage of key-based authentication, the most common use is a persistent password-less connection.
If you installed the PuTTY system via the msi, then all the associations are typically set up for you. Simply double click your private key file and enter your key password to load your key into the agent.
Once loaded, you can double click the icon in the lower right tray and it will show you the fingerprints of the keys you have loaded.
This will allow PuTTY to connect without having to enter your password.
When you are done with your session, please remember to log out or remove the key from Pageant. This can be done easily by double clicking the Pageant tray icon, click the key you want to remove and then click “Remove Key".